Deploy Hashicorp Vault
Vault container in Railway
vault-railway-template
Just deployed
/vault/file

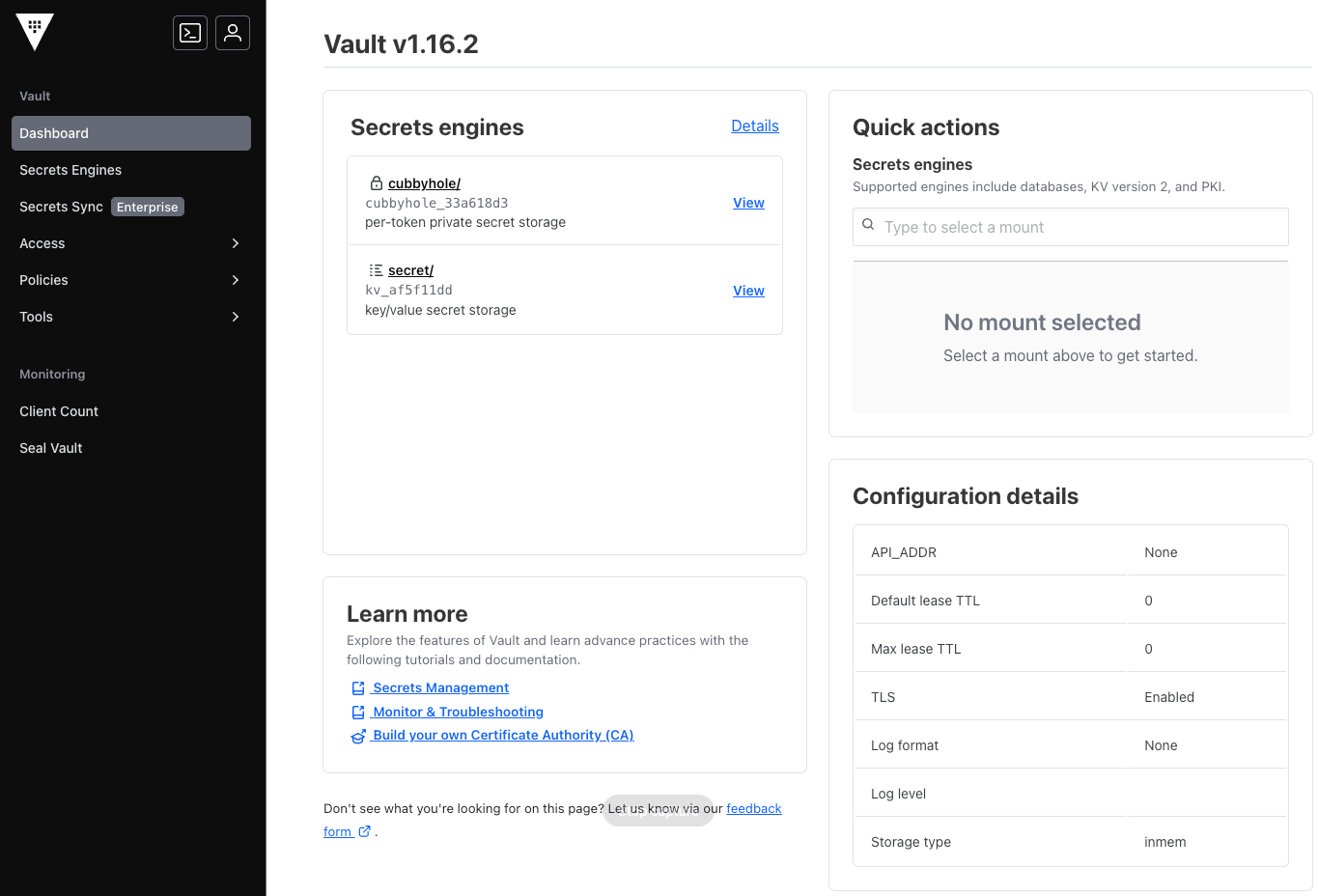
Deploy and Host HashiCorp Vault on Railway
HashiCorp Vault is a secrets management tool that provides secure storage, dynamic credentials, encryption as a service, and fine-grained access control for sensitive data. This template deploys a production-ready Vault server on Railway with sensible defaults and an easy path to scale.
About Hosting HashiCorp Vault
Vault runs as a single service that exposes an HTTP API and an optional web UI for managing secrets, policies, and authentication methods. It can operate in development mode with in-memory storage for quick testing, or in production mode with persistent file-based storage. Railway makes it simple to deploy Vault without managing servers, while enabling vertical scaling and persistent storage for your secrets engine.
Common Use Cases
- Centralized secrets management for applications and infrastructure
- Dynamic credential generation for databases, cloud providers, and services
- Encryption as a service for sensitive data at rest and in transit
- Access control and audit logging for secret operations
Dependencies for HashiCorp Vault Hosting
The Railway template includes all required dependencies: the Vault runtime and configuration. No additional databases or services are required.
Implementation Details
Architecture Components
This template deploys one service:
- Vault Server: secrets engine exposing the HTTP API and optional web UI
Server Configuration
Vault is configured via environment variables at deploy time:
ENV: Set todevfor development mode (in-memory storage) orproductionfor persistent file storagePORT: HTTP listener port (default:8200)UI_ENABLED: Enable or disable the Vault web UISTORAGE_PATH: File-based storage path for production modeDEFAULT_LEASE_TTL: Default lease duration for dynamic secretsMAX_LEASE_TTL: Maximum allowed lease durationDEV_ROOT_TOKEN_ID: Root token for development mode
Development Mode
Running in development mode (ENV=dev) uses in-memory storage. Redeploying, upgrading or restarting the Vault will erase all data.
To avoid data loss, use medusa to export your secrets before upgrading and re-import them afterward.
License Information
HashiCorp Vault is source-available under the Business Source License (BSL 1.1). See the Vault repository for full license details.
Why Deploy HashiCorp Vault on Railway?
By deploying HashiCorp Vault on Railway, you get a centralized secrets management solution with minimal operational overhead, ready to integrate with your existing services.
Notes
Template Content
vault-railway-template
FournyP/vault-railway-template